Introduction
Security Information and Event Management (SIEM) platforms are essential tools for detecting and responding to security threats. These systems can analyse and correlate data from various sources to identify potential threats in real-time. However, SIEM systems can become less effective when attackers use advanced or new techniques to evade detection and if they are not regularly tested and retuned. Attack simulations based on MITRE ATT&CK TTPs can be used to enhance the detection capabilities of SIEM systems by testing their effectiveness against real-world attack scenarios. Let’s look at enhancing SIEM detections with MITRE ATT&CK simulations.
Dr Anton Chuvakin – State of SIEM Detection 2022
What is the MITRE ATT&CK framework?
The MITRE ATT&CK Framework is a framework that provides a comprehensive list of adversarial tactics, techniques, and procedures (TTPs) that attackers use to compromise systems. The framework consists of 12 categories of tactics and 200+ techniques that can be used to achieve the objectives of an attack. The MITRE ATT&CK framework is increasingly used by companies as the foundation of their offensive security testing programmes.
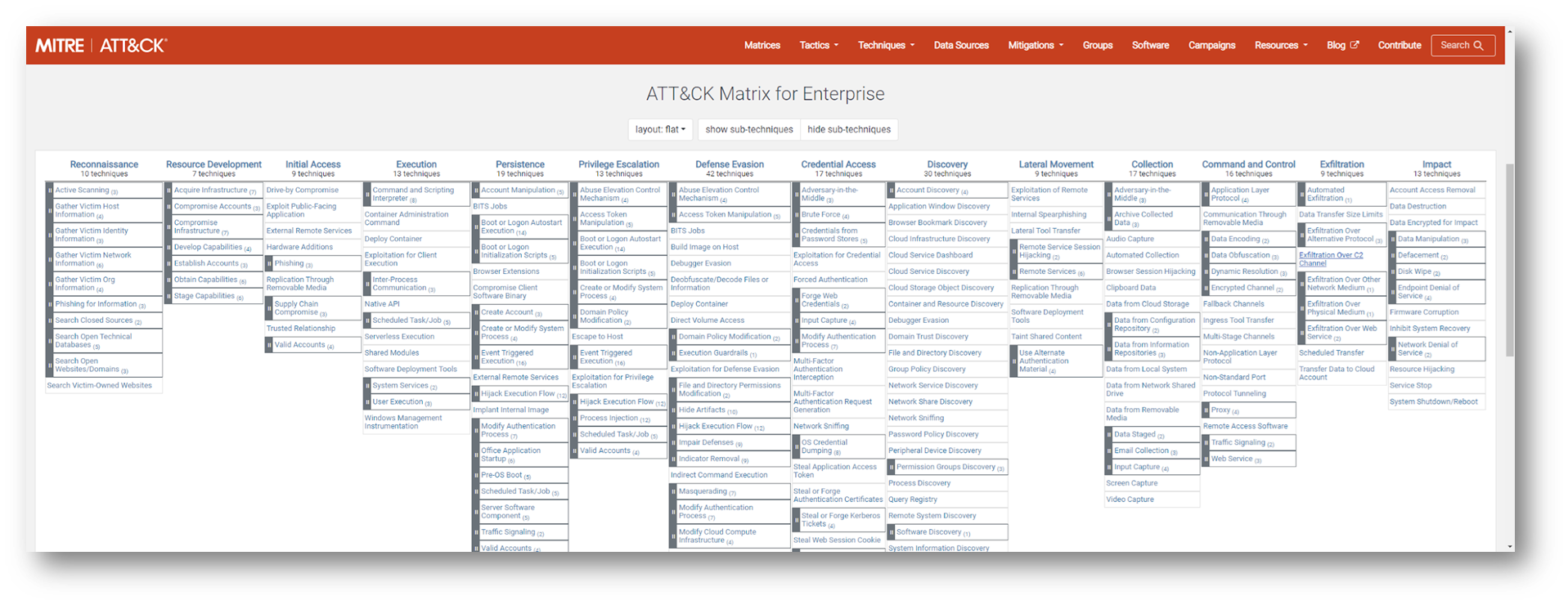
MITRE ATT&CK Framework courtesy of MITRE
Using MITRE ATT&CK TTPs to enhance SIEM Detection Capabilities
SIEM platforms increasingly make use of MITRE ATT&CK TTPs to identify and map adversarial behaviours. Using attack simulations based on MITRE ATT&CK TTPs can therefore be an effective way to stress test a SIEM’s detection configurations and to ensure that the security team is able to detect potential threats quickly. By simulating these attacks, security teams can identify gaps in their detection capabilities and fine-tune their SIEM systems to detect and respond to these attacks.
For example, MITRE recommends that organisations regularly test their defences against the MITRE ATT&CK Top 10. This is a list of the most used adversarial techniques used by threat actors. Conducting these tests can be carried out using professional services based Red Team testing, but these tests can be expensive and potentially disruptive to the business. For this reason, they are also often rarely conducted on a frequent basis with many companies only conducting such tests once a year or to satisfy regulatory or other compliance requirements.
Breach & Attack Simulation (BAS) tools, like Validato, offer the possibility to simulate these kind of adversarial behaviours much more frequently than manual Red Team testing and without causing any damage or disruption to the network. Data produced by BAS platforms is unbiased and can be used by security teams to engineer their SIEM platforms to be able to detect threat behaviours more effectively.

Using Validato to simulate the MITRE Top 10 adversarial techniques
Another example of using MITRE ATT&CK TTPs to enhance SIEM detection capabilities is by simulating a ransomware attack. A ransomware attack typically involves multiple stages, including initial access, command and control, lateral movement, and data exfiltration. By simulating these stages, security teams can test their SIEM system’s ability to detect and respond to these attacks. For example, the SIEM system can be configured to detect unusual network traffic associated with the command and control stage (T1071), unusual user behavior associated with lateral movement (T1570), and data exfiltration (T1048).
Top SIEM platforms miss detections for 80% of MITRE ATT&CK TTPs
Research published by CardinalOps in May 2022 suggests that Enterprise SIEMs are missing detections for 80% of all MITRE ATT&CK techniques.
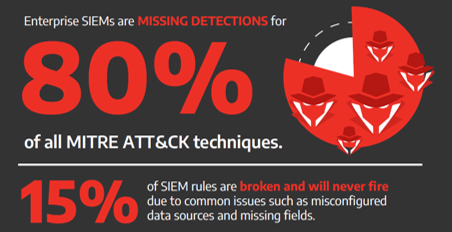
CardinalOps – Enterprise SIEMS missing detections for 80% of MITRE ATT&CJ Techniques
The implications of this research is hugely significant because what CardinalOps is saying is that for many companies running leading SIEM platforms, they are effectively flying blind and that the data presented to them on-screen cannot be relied on. CardinalOps does point out that this is not because the SIEM platforms that they assessed are not capable of detecting MITRE ATT&CK techniques, but is rather due to the fact that SIEM platforms tend to be highly complex and require constant tweaking and configuration in order to ensure that they are able to detect the right behaviours. In many cases, they may be configured when first deployed and then not re-tested and configured again.
How to use Validato to enhance SIEM detections using MITRE ATT&CK
Validato was designed to be a cost effective and easy way for IT and Information Security teams to be able to safely and regularly test the effectiveness of their security controls and SIEM detection capabilities.
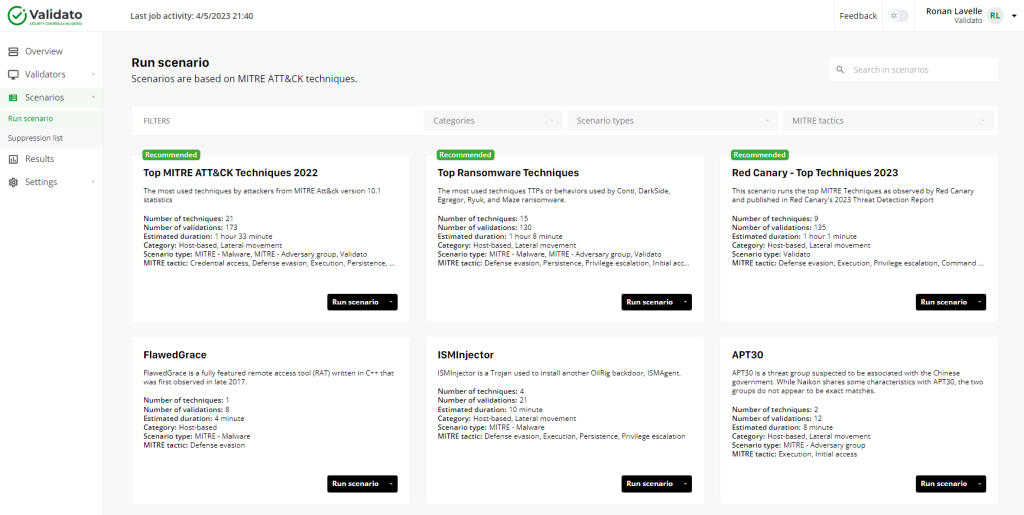
Validato – Simulating MITRE ATT&CK techniques
Cyber threat scenarios based on MITRE ATT&CK TTPs can best tested without having specialist offensive security testing knowledge or skills from within the Validato platform. The attack simulations are designed to be safe to run in production and the results are available within a matter of minutes.
The results data is completely unbiased and provides clear information on the following:
- Did security controls block or not block Validato’s behavioural simulated threats?
- Did the SIEM detect or not detect Validato’s behavioural simulated threats?
If the SIEM platform did not detect particular TTPs, then full information is provided to reconifigure and retune the SIEM and other enterprise controls to ensure that these will be detected in the future.
Conclusion
In conclusion, using MITRE ATT&CK TTPs to simulate real-world attacks can be an effective way to enhance the detection capabilities of SIEM systems. By testing their SIEM systems against these attacks, security teams can identify gaps in their detection capabilities and fine-tune their systems to detect and respond to these attacks more effectively.


