In today’s digital landscape, where cyber threats continue to evolve and grow in complexity, the importance of cybersecurity cannot be emphasized enough. Organizations across various sectors face the constant risk of cyber attacks, which can have severe consequences ranging from financial losses to reputational damage. To effectively combat these threats, cybersecurity professionals employ a range of strategies, one of which is cyber attack simulation. But what is a cyber attack simulation? Continue reading to find out more.
Understanding Cyber Attack Simulations: Definition and Purpose
Cyber attack simulation, also known as red teaming, is a controlled and planned exercise conducted by cybersecurity experts to mimic real-world cyber attacks.
The primary purpose of a cyber attack simulation is to:
- evaluate an organization’s security posture,
- validate the effectiveness of security controls,
- test detection capabilities, and
- assess the effectiveness of their incident response capabilities.
The aim of a cyber attack simulation is to test the cyber resilience of an organization and its ability to detect adversarial behaviors and to prevent them. Attack simulations should be run frequently for optimum risk assurance.

Validato – Cyber Attack Simulation Platform
Three Questions to ask When Planning a Cyber Attack Simulation
The process of conducting a cyber attack simulation involves a systematic approach to evaluating an organization’s cybersecurity defenses and response capabilities. It is a controlled exercise that mimics real-world cyber attacks, allowing cybersecurity professionals to identify vulnerabilities, test incident response plans, and enhance overall resilience. By understanding this process, organizations can proactively assess their security posture and take measures to mitigate potential risks. Here are three questions to ask yourself when planning to conduct a cyber attack simulation:
- What are we testing? Cyber attack simulations should be based on threat scenarios that are important to your business. A useful place to start should be cyber risks that are identified in your organization’s corporate risk register.
- Where do we want to conduct the attack simulation? When running a cyber attack simulation it is important to take a risk based approach and start by running attack simulations in the highest priority areas of your business.
- Who is being targeted? Is it your assumption that low privileged users should not be able to access data and systems outside of their organizational area? If so, you should test your hypothesis using different levels of user privilege when executing a cyber attack simulation.
Benefits of Cyber Attack Simulations
Cyber attack simulations offer a range of valuable benefits for organizations seeking to strengthen their cybersecurity defenses. By subjecting their systems, networks, and personnel to simulated attacks, organizations can gain valuable insights and improve their overall security posture. Understanding these benefits empowers organizations to leverage cyber attack simulations as powerful tools in their ongoing efforts to protect against evolving cyber threats.
- Validate the effectiveness of security controls: According to a recent survey from Panaseer organisations manage 76 security controls on average. These controls need frequent re-tuning and configuration in order to detect and protect against evolving cyber threats and adversarial behaviors. However, few security teams have the time or resources to properly maintain the tool-sets that they have. Attack simulation platforms should test a controls ability to block adversarial behaviors and provide advice on how to remediate issues when they arise.
- Test the organization’s detection capabilities: According to CardinalOps many enterprise SIEMs are missing detections for 80% of all MITRE ATT@CK Techniques. This means that organisations could be flying blind and may not be detecting adversarial behaviors effectively. This is therefor imperative that detection capabilities are optimized for a variety of cyber threat scenarios. Regular cyber attack simulations are an effective way to achieve this.
- Testing Incident Response Plans: Cyber attack simulations provide an opportunity to test an organization’s incident response plans and evaluate their effectiveness. By simulating various attack scenarios, organizations can assess how well their teams detect, respond to, and mitigate the impact of an attack. This allows for the identification of any gaps or shortcomings in the incident response process, enabling organizations to refine and improve their strategies.
- War-gaming: Attack simulations serve as a useful test bed for security personnel to train and develop their knowledge and skills in realistic cyber attack environments without causing harm or disruption to the business.

Cyber War-Gaming, Courtesy of TechTarget
Challenges and Limitations of Cyber Attack Simulations
While cyber attack simulations offer significant advantages, they also come with their own set of challenges and limitations. Ethical considerations, such as ensuring the exercise remains within legal boundaries and does not cause unintended harm, are crucial. Resource constraints, including the availability of skilled personnel and budget limitations, may impact the scope and comprehensiveness of simulations. Balancing realism with safety is another challenge, as simulations should accurately reflect potential threats while minimizing the risk of disruptions. By understanding and addressing these challenges, organizations can maximize the effectiveness of their cyber attack simulations and mitigate potential limitations.
- Ethical Considerations: Simulating cyber attacks raises ethical considerations, as there is a potential risk of causing unintended disruptions or harm during the exercise. Organizations must strike a balance between realism and safety to ensure the simulation does not negatively impact regular operations or expose sensitive information. Ethical boundaries should be clearly defined and respected throughout the simulation process.
- Resource Constraints: Conducting effective cyber attack simulations requires significant resources, including skilled personnel, time, and financial investments. Small organizations with limited budgets may face challenges in conducting comprehensive simulations, thus limiting their ability to assess their cybersecurity posture effectively. However, there are cost-effective alternatives available, such as utilizing open-source tools and leveraging external expertise through partnerships or managed services. Alternatively there are a number of automated cyber attack simulation platforms, like Validato, that allow complex threat scenarios to be simulated without the need for dedicated personnel.
- Realism vs. Safety: Creating realistic simulations without compromising safety is a delicate balance. While simulations should accurately reflect potential real-world threats, precautions must be taken to ensure the exercise does not inadvertently cause harm or breach ethical boundaries. Organizations must carefully consider the potential impact of the simulation on their systems, networks, and personnel to strike the right balance between realism and safety.
Best Practices for Effective Cyber Attack Simulations
To ensure the effectiveness and success of cyber attack simulations, organizations should adhere to a set of best practices. Defining clear objectives and desired outcomes is crucial, as it helps focus the simulation and align it with the organization’s cybersecurity goals. Involving key stakeholders from different departments promotes collaboration and a comprehensive evaluation of the organization’s security posture. Realism and relevance are essential aspects, ensuring that simulations accurately reflect potential real-world threats. Thorough documentation and analysis of findings allow for actionable insights and informed decision-making. By following these best practices, organizations can optimize the value and impact of their cyber attack simulations, ultimately enhancing their overall cybersecurity resilience.
- Define Clear Objectives: Before conducting a cyber attack simulation, organizations should establish clear objectives and desired outcomes. This ensures the exercise remains focused and aligns with the organization’s specific cybersecurity goals. Clear objectives also help in determining the scope and parameters of the simulation.
- Involve Key Stakeholders: Effective simulations involve key stakeholders from different departments within the organization, including IT teams, security teams, and senior management. Collaborative participation ensures a comprehensive evaluation of the organization’s security posture and enhances the likelihood of successful outcomes. It also promotes cross-functional understanding and builds a unified approach to cybersecurity.
- Ensure Realism and Relevance: To derive maximum benefit from cyber attack simulations, the scenarios must be realistic and relevant to the organization’s specific industry and threat landscape. Simulations that accurately reflect potential real-world threats provide the most valuable insights. Tailoring simulations to the organization’s unique environment ensures that the exercise addresses specific vulnerabilities and challenges.
- Document and Analyze Findings: Thorough documentation and analysis of the simulation results are crucial for deriving actionable insights. Detailed reports should be generated, outlining the vulnerabilities identified, lessons learned, and recommendations for improving the organization’s cybersecurity measures. These findings serve as a valuable resource for decision-making, remediation planning, and ongoing improvement of the organization’s security posture.
Case Studies: Successful Cyber Attack Simulations
The real-world examples elucidated upon below demonstrate the effectiveness of cyber attack simulations in identifying vulnerabilities, enhancing incident response, and fortifying cybersecurity measures. By examining these case studies, organizations can gain insights and inspiration for conducting their own successful cyber attack simulations.
Simulating a Phishing Attack:
In this case study, a financial institution conducted a phishing simulation to assess its employees’ susceptibility to email-based attacks. The simulation involved sending simulated phishing emails to employees and tracking their responses. The exercise helped identify employees who were prone to clicking on suspicious links and enabled targeted training and awareness programs to mitigate the risk of falling victim to real-world phishing attacks.
Red Team vs. Blue Team Exercise:
A large technology company conducted a red team vs. blue team exercise to simulate a sophisticated network breach. The red team, acting as attackers, attempted to infiltrate the company’s network, while the blue team, responsible for defense, worked to detect and mitigate the attacks. The exercise allowed the organization to identify critical vulnerabilities, strengthen its incident response capabilities, and refine its defensive strategies.
Simulating a Ransomware Attack:
In this case, a healthcare organization conducted a simulated ransomware attack to evaluate its readiness and response to such an incident. The simulation involved emulating a real-world ransomware attack scenario and observing how the organization’s systems, processes, and personnel responded. The exercise revealed weaknesses in the organization’s backup and recovery processes, leading to improvements that would better protect critical patient data in the event of a real attack.
Testing government, industry regulator or threat intelligence-led advisories:
Agencies like the US CISA, the Canadian Cyber Security Centre and the UK’s NCSC, frequently issue highly valuable threat advisories where a cyber threat scenario is deemed to be important and urgent enough to encourage public and private sector organisations to act and test their cyber resilience against the specific threat. Increasingly, cyber threat advisories will include IOCs and MITRE ATT&CK Techniques that should be tested and controls hardened against in the event of a failure to detect or block simulated threats.
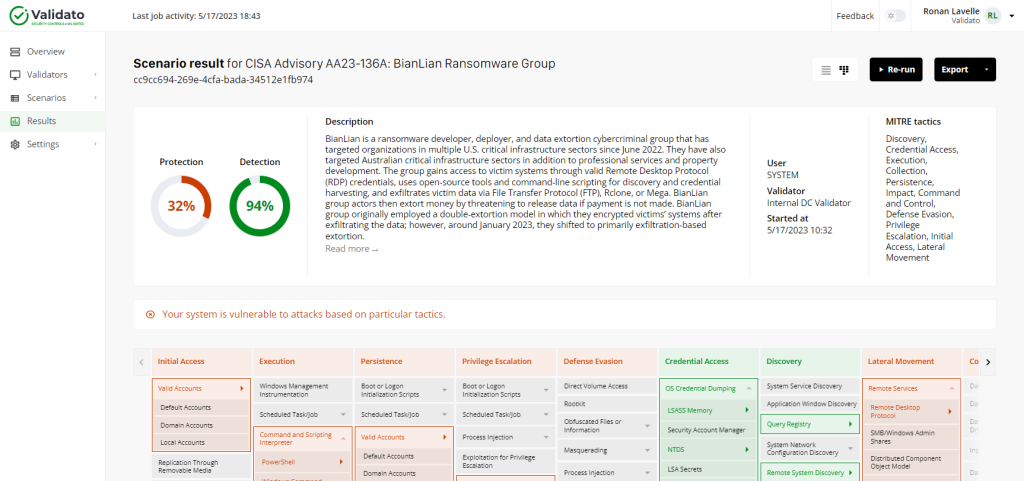
Validato – Ransomware Simulation Test Result
The Future of Cyber Attack Simulations
The future of cyber attack simulations holds promising advancements that can further strengthen organizations’ cybersecurity defenses. Advancements in artificial intelligence and machine learning technologies can enhance the realism and sophistication of simulated attacks, enabling organizations to better prepare for advanced threats. Integration with threat intelligence allows organizations to replicate emerging threats and test their defenses against the latest attack vectors. Continuous testing and automation are key drivers for the future, enabling organizations to conduct simulations more frequently and efficiently.
Advancements in Artificial Intelligence and Machine Learning
The integration of artificial intelligence and machine learning technologies in cyber attack simulations holds great potential. These technologies can enhance the realism and sophistication of simulated attacks, enabling organizations to better prepare for advanced threats. AI and ML algorithms can learn from past attack patterns and dynamically adjust simulation scenarios to mimic emerging threats.
Integration with Threat Intelligence
By integrating threat intelligence into cyber attack simulations, organizations can replicate emerging threats and test their defences against the latest attack vectors. This proactive approach ensures organizations stay one step ahead of evolving cyber threats. Real-time threat intelligence feeds can be incorporated into simulations, enabling organizations to test their response to the most current and relevant threats.
Continuous Testing and Automation
The future of cyber attack simulations lies in continuous testing and automation. With automated tools and platforms, organizations can conduct simulations more frequently and efficiently, allowing for ongoing assessment and improvement of their cybersecurity measures. Continuous testing ensures that security controls remain effective in the face of changing threats and vulnerabilities.

Continuous Testing & Automation – Validato
Conclusion
In an increasingly interconnected world, cyber attack simulations play a vital role in helping organizations strengthen their defenses against evolving threats. By mimicking real-world attacks, organizations can proactively identify vulnerabilities, test incident response plans, and enhance their overall cybersecurity posture.
While challenges exist, advancements in technology and best practices will continue to improve the effectiveness and realism of cyber attack simulations, bolstering organizations’ resilience in the face of cyber threats.
By embracing the power of simulations, organizations can stay ahead of cyber criminals and better protect their valuable assets.



Leave A Comment