In our increasingly interconnected world, the security of telecommunications infrastructure has never been more critical. As technology advances, so do the threats and vulnerabilities that can compromise the integrity and privacy of communications networks. The continuous evolution of technology has led to a greater dependence on telecommunications systems for various aspects of our daily lives. This ranges from personal communications and business operations to critical infrastructure functions. With the growing complexity of these networks, the potential points of entry for malicious actors seeking to exploit vulnerabilities have also expanded. Telecoms are becoming an ever-more attractive target for cyberattacks. To address these concerns, the United Kingdom has implemented the Telecommunications Security Code of Practice. Understanding the Telecommunications (Security) Act has become vital. In this blog post, we will delve into the key aspects of the UK Telecommunications (Security) Act 2021 and explore the challenges it poses for the industry.
Key Components of the Code of Practice
The UK government has implemented a fresh security framework via the Telecommunications (Security) Act (TSA), which officially took effect on October 1, 2022. This novel framework outlines a strong security standard aimed at enhancing the durability and trustworthiness of vital telecommunications networks within the United Kingdom. This development is poised to instigate a substantial transformation across the entire telecommunications landscape, both within the UK and in the broader international context.
The key components of the framework are:
- Risk Management: One of the fundamental principles of the code is the assessment and management of risks. Telecommunications providers are required to identify potential threats and vulnerabilities within their networks and develop strategies to mitigate them. This includes regular testing, security audits, and incident response planning.
- Supply Chain Security: With the increasing reliance on global supply chains for telecommunications equipment, the code places a strong emphasis on supply chain security. Providers are encouraged to assess the security of their supply chain partners and ensure the integrity of the hardware and software they use.
- Network Design and Resilience: The code stresses the importance of designing telecommunications networks with security and resilience in mind. Providers are expected to implement measures that can withstand various threats, including cyberattacks, physical damage, and natural disasters.
- Transparency and Accountability: Transparency is a key element of the code, with providers required to be open and honest about their security practices. They are also expected to cooperate with government authorities and share information on security incidents when necessary.
- Government Engagement: The code promotes collaboration between telecommunications providers and government agencies. This includes sharing threat intelligence, participating in security exercises, and working together to address emerging threats.
Challenges and Obligations Faced by the Industry
The new Telecommunications Security Act imposes a duty on the telecom providers to deploy and enhance a wide range of security controls within their own organization and in key suppliers, and to take proactive risk measures in response to security compromises.
- Ensuring the security of networks and services, encompassing network architecture, governance, risk management, safeguarding of data and network functions, as well as fortifying specific tools essential for monitoring and analysis.
- Conducting regular assessments to facilitate provider understanding of the security status of their networks and services, fostering incentives for continual enhancements in line with evolving risks.
- Upholding competency levels to guarantee that responsible individuals within telecoms companies adeptly comprehend and manage risks.
- Comprehensive testing requirements and guidance to evaluate the vulnerabilities of providers’ networks and services.
- Facilitating cooperation to promote information sharing among public telecom providers while simultaneously mitigating security compromises.
Addressing these challenges requires a collaborative effort between governments, telecommunications industry stakeholders, and cybersecurity experts to develop and implement effective security measures while maintaining the functionality and competitiveness of telecommunications networks and services.
The full range of security requirements is detailed here.
Compliance
The telecommunications industry is now on the brink of a shift in its focus. It will move away from isolated, compliance-oriented security initiatives and, instead, adopt a more proactive, threat-driven approach to securing the telecommunications sector. This fundamental shift distinguishes the TSA from other impactful legal frameworks, such as GDPR, and represents a significant change in how security is addressed within the industry.
The Act segregates the organisations that are covered into three tiers. Organizations are judged principally by their annual turnover as an indicator for the impact that any downtime they may experience would have on it’s ability to continue to operate business as usual. Tier one are companies with a turnover of more than £1bn, tier two have turnovers above £50m, and tier three have turnovers of less than £50m.
While the Act is now operational, it includes time for organisations to make the necessary changes for compliance. Understanding the Telecommunications (Security) Act has truly never been more important:
- Tier one companies have just under a year (until 31 March 2024) to implement the “most straightforward and least resource intensive measures,” and an extra year (31 March 2025) to implement the more complex parts of the requirements.
- For tier two operators, they get an extra two years on each of these days.
- Tier three have no specific deadline, but are instead “strongly encouraged” to “take appropriate and proportionate measures” and to use the code of practice as a guide.
With the focus on incentivizing best practice, of course there are fines for non-compliance. Fines can cost up to 10% of a company’s annual turnover plus up to £100,000 a day for ongoing contravention.
Breach & Attack Simulation (BAS) Tools & Testing Requirements of the TSA
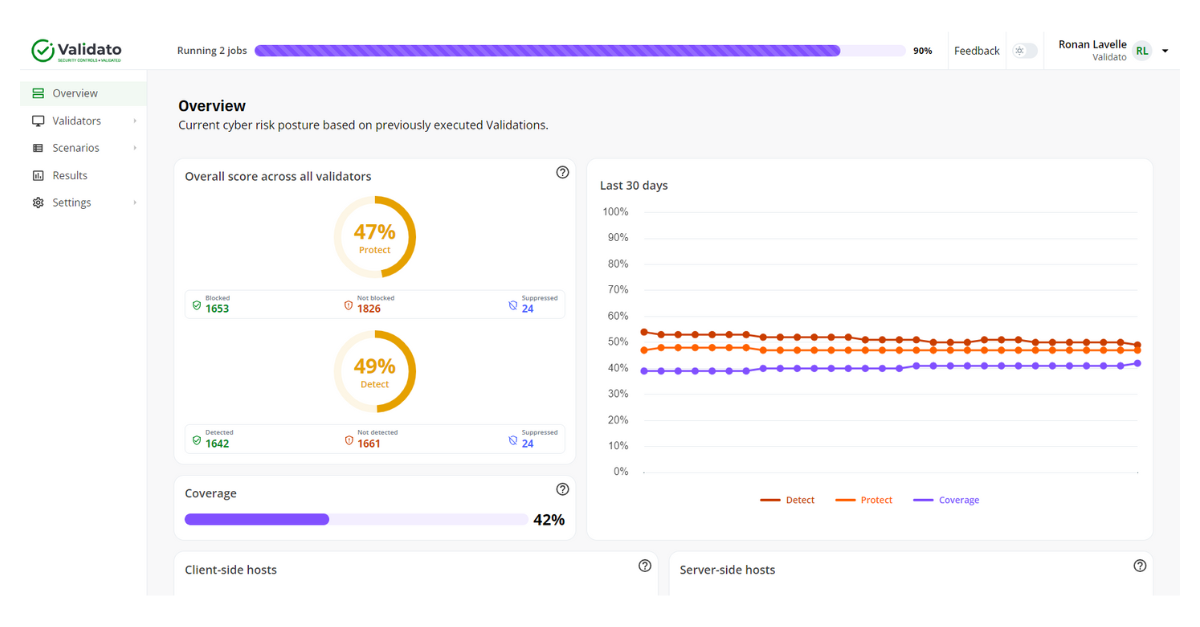
BAS tools can help to address the cyber threat resilience testing requirements of the TSA. BAS tools, like Validato, simulate threat actor behaviours in order to validate the effectiveness of security controls. BAS tools often use the MITRE’s ATT&CK framework as a baseline.
Breach and Attack Simulation tools provide unbiased data that can be used to measure:
- The effectiveness of security controls in safeguarding against both historical and contemporary cyber threats.
- The proficiency of security operations and incident response teams in identifying attack methodologies.
- The organization’s efficiency in responding to and rectifying identified issues.
Validato allows security teams to test and simulate adversarial behaviours relating to identified threats. The telecommunications sector (and its supply chains) can benefit from using Validato. This is due to its ability to validate the effectiveness of security controls and cyber resilience against identified threats. Understanding the Telecommunications (Security) Act is made easy with Validato.
To find out more about Validato, visit www.validato.io, or contact us here.