On May 16th 2023, the US Cybersecurity and Infrastructure Security Agency (CISA) and the Australian Cyber Security Centre (ACSC) issued a joint advisory (Advisory AA23-136A) on the emergence of a new Ransomware group, calling themselves BianLian (after the infamous Chinese theatrical costume dances). BianLian Ransomware has been active in a variety of industry sectors in the United States and Australia, at the time of writing. We are delighted to say that Validato customers can now safely simulate BianLian Ransomware MITRE ATT&CK Techniques to test and validate security control effectiveness and detection capabilities. Read more about Simulating BianLian Ransomware to test defences below:
About BianLian Ransomware Group
BianLian is a ransomware developer, deployer, and data extortion cybercriminal group that has targeted organizations in multiple U.S. critical infrastructure sectors since June 2022. They have also targeted Australian critical infrastructure sectors in addition to professional services and property development. The group gains access to victim systems through valid Remote Desktop Protocol (RDP) credentials, uses open-source tools and command-line scripting for discovery and credential harvesting, and exfiltrates victim data via File Transfer Protocol (FTP), Rclone, or Mega. BianLian group actors then extort money by threatening to release data if payment is not made. BianLian group originally employed a double-extortion model in which they encrypted victims’ systems after exfiltrating the data; however, around January 2023, they shifted to primarily exfiltration-based extortion.
Here is a sample ransom note left behind by BianLian on a victim’s computer:
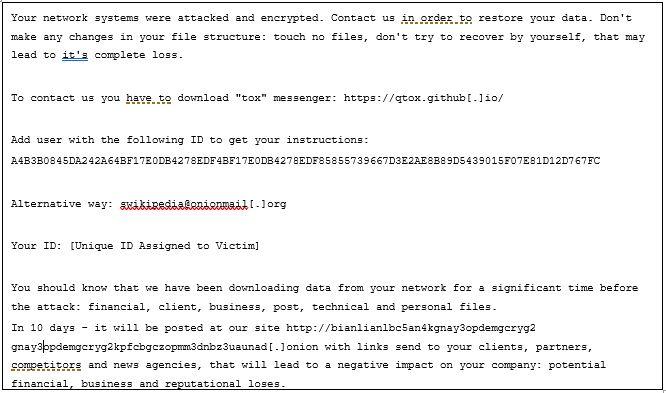
BianLian ransom note
BianLian MITRE ATT&CK Techniques
The following table outlines the key behaviours and techniques of the BianLian Ransomware group, mapped to MITRE ATT&CK techniques. These Techniques are available in the Validato platform to safely simulate and test cyber defences.
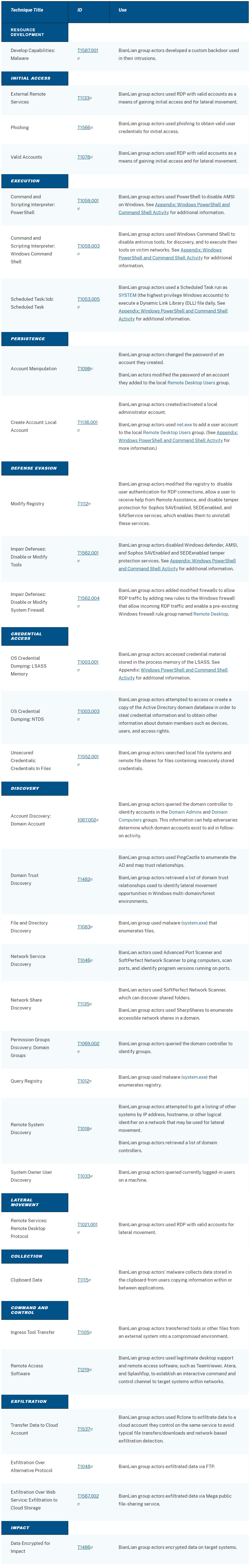
BianLian MITRE ATT&CK Techniques mapped to Validato
Testing your defences against BianLian in Validato
Validato customers can test their security controls and detection capabilities against BianLian behaviours and techniques instantly.

Validato – simulation scenario for BianLian Ransomware Techniques
Here is a summary of the test results in Validato, reporting on overall Protection status and Detection status.

Validato – BianLian threat simulation test results
In addition to regularly validating your defences with tools like Validato, here are CISA’s top level remediation actions to take:
- Strictly limit the use of RDP and other remote services
- Disable command-line and scripting activities and permissions
- Restrict usage of PowerShell and update Windows PowerShell or PowerShell Core to the latest version
Request a trial of Validato
#stopransomware



Leave A Comment