On a daily basis, security teams are confronted with the challenging responsibility of detecting and overseeing security vulnerabilities within their expanding attack surface. Ongoing digital transformation projects, the migration to cloud infrastructure, corporate mergers and acquisitions, and various other IT environment alterations consistently introduce the business to fresh risks. Enter Security Controls Validation – an indispensable component of a robust cybersecurity strategy. Improving cyber resilience with Security Controls Validation is an attainable ideal. In this guide to Security Controls Validation, we delve into the nuts and bolts of Security Controls Validation, its significance, and how it outperforms traditional security testing methods.
Defining Security Controls Validation
Security validation entails the safe simulation of actual attacks on your systems, aiming to uncover weaknesses like misconfigurations, exploitable software vulnerabilities, or vulnerable credentials. By adopting an adversarial perspective, organizations can effectively assess their resistance to attacks and pinpoint areas for improvement before they become targets for exploitation.
Organizations must consistently assess the effectiveness of their security measures in light of evolving threats and shifting attack vectors. Relying solely on human penetration testers and red teams is insufficient to meet the needs of enterprise-scale, frequent testing.
The solution lies in automation, employing a virtual team of offensive security testers capable of emulating the adversarial behaviors deployed by malware and threat actors. With findings available within hours, not days or weeks, organizations can swiftly address high-priority issues based on their risk impact, and retest immediately to ensure the efficacy of implemented changes.
Security Controls Validation, at its core, involves the continuous evaluation of an organization’s security measures to ascertain their efficacy against an assortment of cyber risks. It’s akin to a monthly health check-up for your organization’s cybersecurity infrastructure, ensuring that your security controls are performing optimally and that your defenses are up to the task of thwarting both current and emerging threats.
The Vital Role of Security Controls Validation
According to recent studies, the average enterprise utilizes around 80 different security tools. However, simply layering these tools does not guarantee effective security. Adopting multiple tools also doesn’t necessarily improve security response, and may achieve the opposite effect, according to the Ponemon Institute’s 2020 Cyber Resilient Organization Study. To address this issue, organizations need to focus on high-level security controls validation. By implementing an effective Security Controls Validation solution, enterprises can identify misconfigurations and remediate them before attackers exploit them.
These solutions not only provide a definitive assessment of overall security strength but can also minimize financial and reputational risks. By continuously testing security measures, organizations can stay prepared in the ever-changing cybersecurity landscape. It is crucial to select a security validation solution that assesses the viability of controls, provides continuous validation, and considers the adversarial behaviors of attackers. “More is better” is not always the case when it comes to security tools. Security Controls Validation plays a crucial role in fortifying an organization’s cybersecurity posture, ensuring compliance with industry regulations, and fostering a culture of continuous improvement.
The Key Benefits of Security Controls Validation
Differentiating Between Security Controls Validation and Traditional Security Testing
Security Controls Validation stands apart from traditional security testing methodologies like penetration testing, red teaming, and vulnerability scanning. The key differentiators are:
- Continuous and Automated Assessments: Unlike traditional testing methods, which typically involve point-in-time evaluations, Security Controls Validation provides continuous and automated assessments of an organization’s security controls.
- Threat-informed Defense: Security controls validation testing should be tested within the context of a known or likely threat scenario. Testing should cover all of the adversarial techniques and behaviors related to the specific threat scenario. You can read more about how Validato enables threat-informed defense initiatives here.
- Real-world Attack Simulations: Security Controls Validation uses real-world attack scenarios to test the performance of security controls. This approach offers a more comprehensive and up-to-date understanding of an organization’s security posture.
- Holistic Evaluation: Security Controls Validation offers a holistic evaluation of an organization’s security posture, testing the effectiveness of security controls across multiple layers of prevention and detection.
Key Components of an Effective Security Controls Validation Program
An effective Security Controls Validation program is characterized by several key components:
- Robust Threat Intelligence. A powerful Security Controls Validation program harnesses up-to-date and accurate cyber threat intelligence (CTI) to simulate real-world attack scenarios and techniques.
- Comprehensive Testing Methodology. An effective program employs a comprehensive testing methodology that covers various attack vectors, security controls, and stages of the cyber kill chain. Basing a testing methodology on MITRE ATT&CK, for instance, is an increasingly popular option.
- Continuous and On-Demand Assessments. A robust program offers both continuous and on-demand assessments, enabling organizations to maintain an up-to-date security score.
- Automation and Scalability. An effective program harnesses automation and scalability to efficiently assess numerous security controls across multiple environments.
- In-Depth Analysis and Reporting. An effective program provides in-depth analysis and reporting that includes not only the identification of vulnerabilities and weaknesses but also actionable recommendations for improvement.
- Integration with Security Frameworks. A robust program seamlessly integrates with established security frameworks, such as the MITRE ATT&CK Framework or NIST Cybersecurity Framework.
- Customization and Flexibility. A robust program offers customization and flexibility to adapt to an organization’s specific needs, risk tolerance, and unique security architecture.
Identifying and Prioritizing Critical Security Controls for Validation
Identifying and prioritizing critical security controls for validation requires a methodical and data-driven approach. By conducting Security Controls Validation simulations and analyzing the results, organizations can prioritize their security controls based on the criticality of their assets, threat vectors, and compliance requirements.
Breach and Attack Simulation tools are often deployed to validate security control effectiveness and to test and optimize detections. Penetration testing will normally involve manual attempts to exploit vulnerabilities in order to gain unauthorized access. Ronan Lavelle, Co-Founder at Validato
Most Breach and Attack Simulation (BAS) tools, like Validato, will help information security teams to validate the effectiveness of their security controls and help security operations to better detect threats. Manual penetration and Red Team tests rarely include security control effectiveness within the scope of their testing. Often, the scope of a penetration test will be defined and restricted in advance, in order to keep costs and complexity down. Automated Breach and Attack Simulation tools however, are able to simulate a wide range of attacker behaviours and do this across the whole organization and on a much more regular schedule than manual penetration tests.
Enhance Your Cyber Resilience with Validato
It’s worth noting here that continuous security controls validation isn’t intended to replace other cybersecurity measures. However, it can form a crucial part of a holistic cyber security operations model. The goal is to mimic potential breaches or attacks, which helps companies stay up-to-date on their cyber defense strategies. Also, when used in conjunction with real-time threat detection and response (containment and isolation), these simulations can help move companies towards a stronger security posture.
As cyber threats evolve, it’s essential for organizations to be equipped with proactive security solutions that can keep up with these changes. Validato‘s BAS platform is a game-changer in the realm of security validation. It comprehensively tests each MITRE ATT&CK Technique related to a specific threat scenario and reports on how enterprise security controls were able to detect and/or protect the business from the threat.
Operating in a safe manner akin to a real attacker, this platform conducts comprehensive, real-time security validation. It also offers guidance on remediation and prioritization of the most crucial issues. In today’s cybersecurity landscape, Validato is a necessity to ensure your organization’s readiness for tomorrow’s challenges.
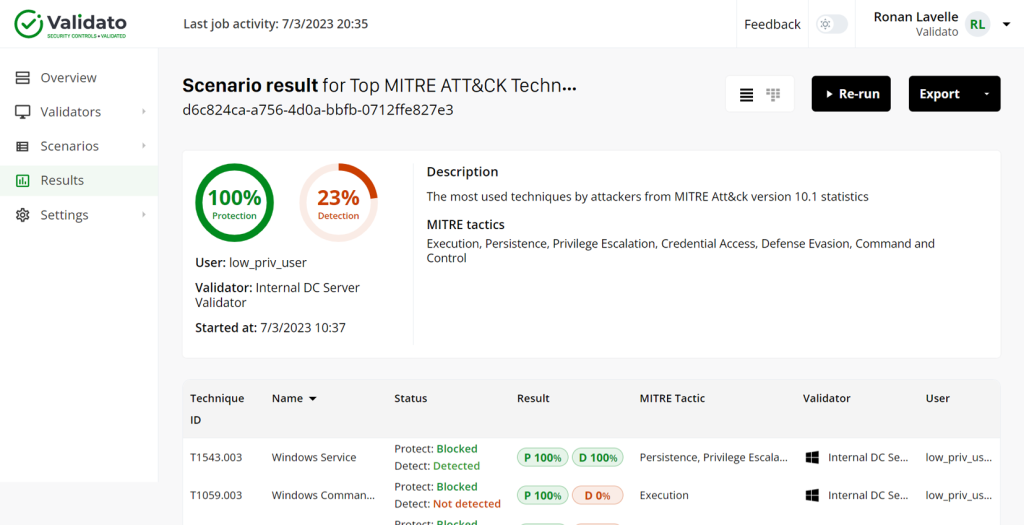
The Validato Platform
Conclusion
Data breaches are dangerous, especially to small and medium-sized businesses.
In fact, 60% of small companies that suffer data breaches end up going out of business within six months. That’s why it’s important for businesses to take a proactive approach to cyber security. It means making sure you’ve updated your software, conducted penetration tests, and are aware of how to avoid potential threats. Security Controls Validation is an essential part of an organization’s cybersecurity strategy. By conducting regular Security Controls Validation exercises, organizations can ensure that their security controls are effective. This in turn, will aid in combating rapidly changing cyber threats. It’s an ongoing process that ensures your organization’s cybersecurity infrastructure is fully equipped to deal with the persistent and escalating threats of the digital age.
Security Controls Validation involves safely emulating real attacks against your systems. This will reveal weaknesses such as misconfigurations, exploitable software vulnerabilities and at-risk credentials. By adopting the adversary perspective, organizations can accurately measure resilience to attacks and identify remediable gaps before exploitation.
Improving Cyber Resilience with Security Controls Validation has never been easier. Find out how cyber-resilient your business is against top ransomware scenarios. Contact the knowledgeable team at Validato to book an obligation free discussion.


